Segmented infrastructure with documented recovery paths.
Policy authority, VLAN legibility, and operator runbooks are treated as one delivery package so the network stays quiet after handover.
Oregon · Remote · Discreet by Design
Security. For Surety. For estates, operating businesses, and internal teams that need analytics, automation, web, and network systems that stay dependable under pressure.
Baud Haus Ops delivers architecture analysis, analytics systems, agent workflows, web platforms, and network reliability with clear scope, documented delivery, and clean handover.
Primary Engagement Lanes
Current-state technical and operational audits that surface bottlenecks, risk, and modernization paths before implementation spend.
02 // VESPERAuthority websites, CMS governance, performance engineering, and conversion infrastructure that your team can operate independently.
03 // ORBITMeasurement architecture, event governance, and executive-ready dashboards that replace guesswork with accountable signal.
04 // VECTOROperational automation, runbook codification, and scoped agent workflows that increase throughput without creating hidden dependencies.
Proof is presented as operating evidence: intervention, measurable delta, and handover condition. If it cannot be evidenced, it is not proposed.
Archive Protocol
Each proof surface records what changed, why it changed, and what the next operator receives on day one.
Policy authority, VLAN legibility, and operator runbooks are treated as one delivery package so the network stays quiet after handover.
Performance, search architecture, analytics events, and operating docs are specified together so the system remains governable by the next operator.
Archive Notes
Best Fit
Not a Fit
These ranges are planning anchors, not fixed quotes. Final scope is itemized by complexity, constraints, dependencies, and risk surface.
Foundation
$8K - $24K typical scope
For single-surface initiatives: web rebuilds, segmented network deployments, analytics baselines, and hardening passes.
Core
$24K - $65K typical scope
For integrated web, network, and measurement initiatives with clear handover package and operational runbooks.
Flagship
$3.5K - $12K / month
For ongoing strategic ownership, monthly optimization cycles, and high-discretion support in active operations.
Engagements are scoped per project with acceptance criteria up front. No discovery theater, no ambiguous handoff.
Engagement starts with a written brief so constraints, objective, and context are explicit before any scope discussion.
A short scope memo defines deliverables, timeline, and acceptance criteria before implementation starts.
OSINT and Security work require written authorization and verified control over target scope. No exceptions.
Runbooks, documentation, and repository transfer are treated as deliverables, not optional extras.
Surety Delta
Excellent from afar, cosmological at close range: pressure, exposure, and operational delta in one compact strip.
Feed policy: no Kaspersky, no Russian telemetry sources, no heavy external embeds.
Live + modeled threat pressure, tuned for explainability.
Signal Integrity Meter
A1
Integrity stabilized
Live probes/min
2,899
Blocked patterns/hr
407
WAF blocks/hr
263
External abuse intelligence overlays for routing and perimeter context.
Signal Integrity Meter
B2
Integrity monitored
DROP CIDRs
976
C2 IPs
409
DNS sinkholes/hr
33
Web-app and exploit exposure indicators translated to business impact.
Signal Integrity Meter
A0
Integrity confirmed
KEV watchlist
1,361
Critical advisories/24h
18
Pattern blocks/hr
407
BHO operating pulse (from weekly analytics snapshot)
Signal Integrity Meter
A1
Integrity stabilized
Visitors
409
CTA events
129
Who This Is For
The operating model serves clients across the Eugene, Portland, and Ashland corridor, with remote execution nationwide. Engagements range from private estates to operating companies, scoped to match business goals and budget.
BHO-NOTE(1) // Fit Signal
Best outcomes come from clear scope, practical timelines, and systems that remain operable after handover.
Reliable property-wide infrastructure, guest isolation, surveillance integration, and remote operational visibility.
Booking, POS, staff access, and guest connectivity shaped into one stable operational system.
Web, analytics, and automation infrastructure that improves decision speed, lowers operational drag, and supports growth.
Launch-cycle infrastructure and digital surfaces designed for timing, clarity, and controlled throughput.
We do not build for the average case. We build for the moment where ambiguity, downtime, or weak handover becomes operational risk.
Synthesis
Fragmented delivery creates hidden risk. We shape the stack as one system so dependencies are visible and transfer is clean.
Evidence
Architecture choices, analytics, and operating controls are designed to produce legible proof, not verbal reassurance.
Stewardship
Documentation, runbooks, and operating context are deliverables. Lock-in is treated as a design failure.
Every article is written for implementation: clear assumptions, usable sequence, and documented tradeoffs.
Build a practical pfSense + UniFi VLAN architecture with segmentation, Suricata, pfBlockerNG, Pi-hole, and centralized logging from WAN to endpoint zones.
Read note →Design SMB VLAN segmentation that remains maintainable after turnover using role-based segments, clear policy matrices, and handover-ready documentation.
Read note →A decision-support framework for due diligence reports, including confidence context, risk weighting, source traceability, and next actions leadership can use.
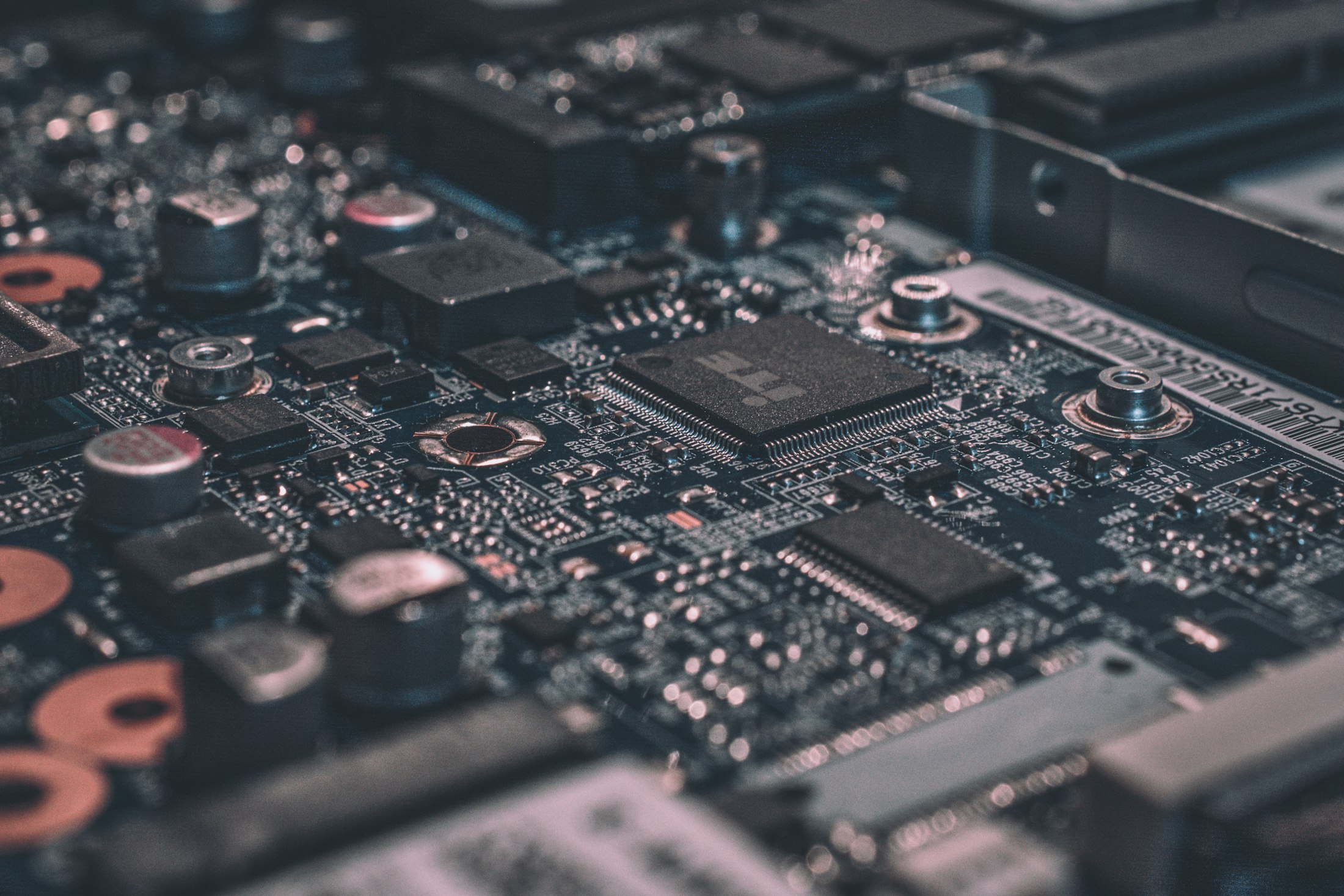
Read note →Visual Language
Visual system built for trust: architectural composition, warm contrast, and material depth without decorative noise.